What is IP Spoofing ?
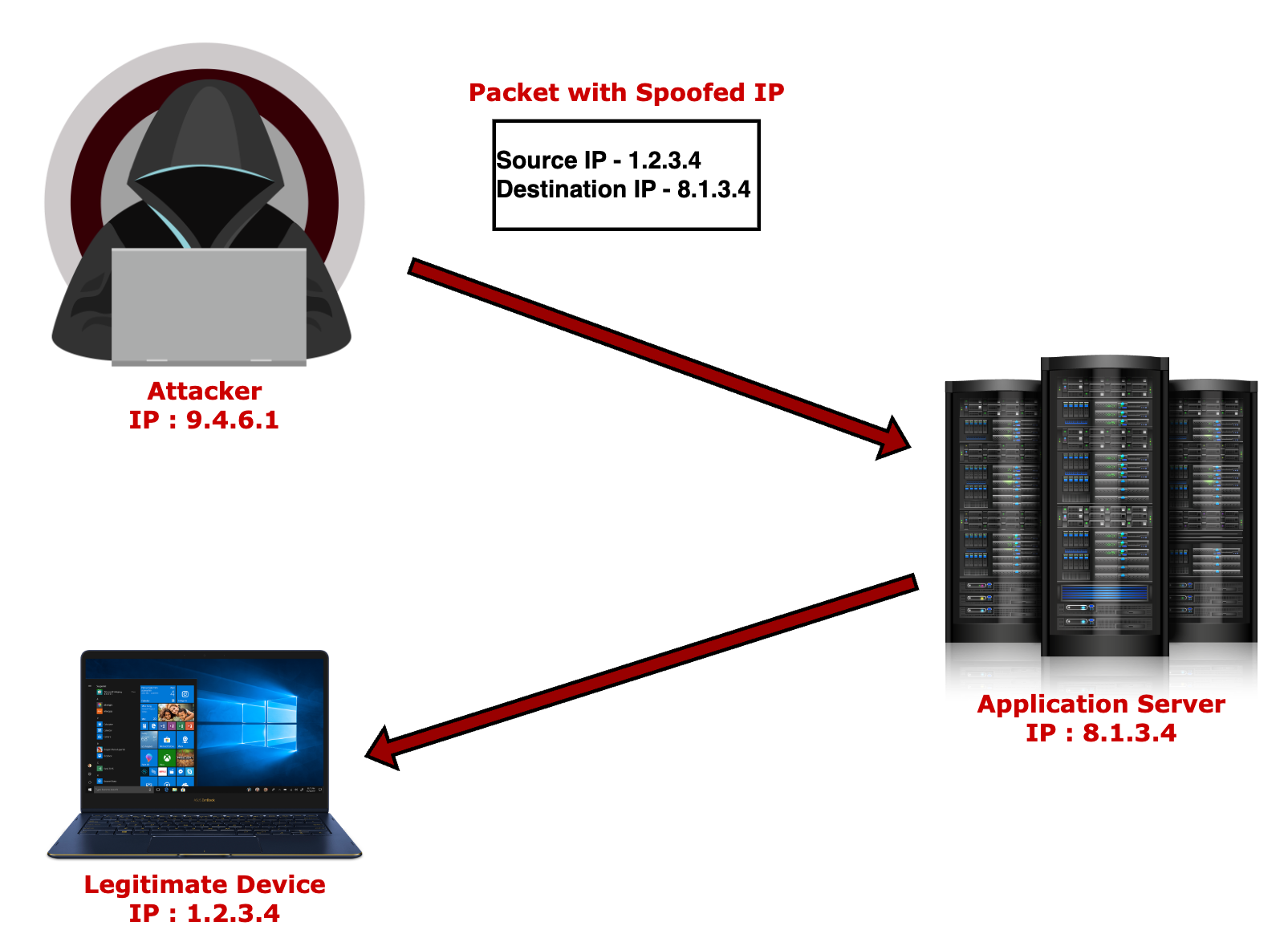
IP Spoofing is creation of IP (Internet Protocol) packets with a fake source IP. This technique allows its operator to impersonate a different device or hide its identity.
IP Spoofing remains one of the most frequently used techniques for operators that launch DDoS attacks.
What is Internet Protocol/IP ?
The primary protocol for exchanging data over computer networks is the Internet Protocol/IP. This protocol in its specification defines each IP packet will contain a header which has the IP address of the sender amongst other things like IP version, Destination IP etc. If you are interested in reading more about the IP protocol please follow this link - https://datatracker.ietf.org/doc/html/rfc791
Why would you perform IP Spoofing ?
Now since this specification enforces the IP address of the sender as a mandatory field in its header an attacker may want to mask their identity thus the need to perform IP spoofing. Imagine if I am launching attacks against your application/website I would likely spoof the source IP in a dynamic/random manner to avoid being caught by the security systems in place. This ensures I have masked my identity and would make it very difficult for your security systems to block me as you cannot block by source IP since you would end up blocking a lot of legitimate IPs, also makes it very difficult for law enforcement agencies to take stringent action against me. This can be a significant advantage that an attacker would want to exploit.
So what is this IP packet that I make a mention of in the above passage ?
An IP packet is the smallest messaging entity exchanged over an IP network. Think of it as one of the foundational blocks of modern networking systems. Every IP packet has a structure which involves certain mandatory fields.
So can we not stop IP spoofing then ?
Yes IP spoofing can be mitigated.
Network Ingress Filtering is a tool used to ensure the incoming packets are actually from the networks from which they claim to originate. This will help mitigate IP spoofing attacks which is one of the most frequently used techniques in DDoS attacks. This packet filtering technique has been used by many ISPs to prevent IP spoofing attacks.
Internet Engineering Task Force(IETF) has defined a Best Current Practices(BCP38) document written all the way back in 2000 on Network Ingress Filtering - block packets which have forged source IP addresses(IPs that were not assigned to the device that is sending them).
Great! We now know there is a technique that helps prevent IP spoofing attacks, however we do not see all ISPs employing this technique widely(strangely). Why ?
There are multiple reasons why certain ISPs do not employ this technique to this day -
- If the ISP does not have equipment that allows them to filter IP spoofing packets then they would have to make a decision on installing one, Is it worth it though ? DDoS attacks are launched against a target which has nothing to do with the ISP in almost all scenarios so why would an ISP go out and spend money and assign resources to install and maintain an equipment to help solve a problem it does not see directly impacting it.
- Certain ISPs do not have the capability to perform fast switching at the router when IP filtering is turned on. When turned on if it introduces latency then an ISP may not want to use this technique.
- Encapsulation could be another reason why an ISP is not able to perform ingress filtering for IP spoofing.
Are there strong reasons to why an ISP would perform Network Ingress Filtering ?
The answer to this question is a resounding YES! I have highlighted a few reasons below -
- Save Bandwidth, The cost of DDoS attacks can run high. These spoofed packets when they egress the network of an operator/ISP there would a cost attached to them.
- Most/All network operators/ISPs do not want be associated with malicious traffic.
- The cost of installing equipment that can do mass ingress filtering is quite minimal these days. Most carrier grade BGP routers have this capability built in. This overcomes the limitations of some of the older equipment when it comes to filtering.
Note: Many ISPs have now come to the conclusion preventing spoofing attacks can save them money so they are implementing filtering technique to stop such attacks.


0 Comments