The above image depicts first medieval settlers arriving in Iceland.
Before we get into cybersquatting let us first understand the source of this name. So what does squatting really mean ?
Squatting is occupying an abandoned or unoccupied piece of land that you have no rights to. Such illegal occupation happens across the globe and has been written about extensively. These individuals - the squatters are sometimes also referred to as settlers.
Cybersquatting is an illegitimate method of registering, trading or hoarding internet domain names. These registrations are performed with malicious intent.
There are entities/individuals that profiteer from such fraudulent registrations.
Listed below are a few common cybersquatting techniques -
Typosquatting
This is a technique which involves purchasing a domain with a typo/intentional error character/characters.
Now I own this domain - coderevere.com, imagine someone buys a similar domain name with 1 or 2 errors/typos, the intention is to have it look/sound similar to the target domain.
Examples : coderrevere.com , codereveere.com etc.
This is a common technique for phishing scams, imagine an unsuspecting end user tries to visit twitter.com but makes a typo in the browser - rwitter.com, the website comes up, looks almost the same as twitter.com, the perpetrator will try to lure such users into a phishing campaign.
Homoglyphs(also known as Homographs)
This technique involves registering domain names that look similar to the target domain, this similarity could be a result of characters that look similar across different languages OR a digit and a character like 'O' and '0' that bear resemblance etc.
Attackers frequently leverage this technique to lure in unsuspecting users to phishing campaigns. Lets say there is a popular e-commerce website, example.com, the attacker will setup a fake site, exαmple.com, this eerie resemblance leads unsuspecting shoppers to commit to fraudulent transactions, provide sensitive data or be a malware target.
Such brand impersonation can lead to a loss in reputation to the target brand, generally large brands use some kind of Brand Impersonation/Protection offering from a vendor to scan domains/URLs that are set up to commit such illegitimate activities on the world wide web. Security vendors collect this data and initiate a legal request to takedown such fraudulent websites, email services etc.
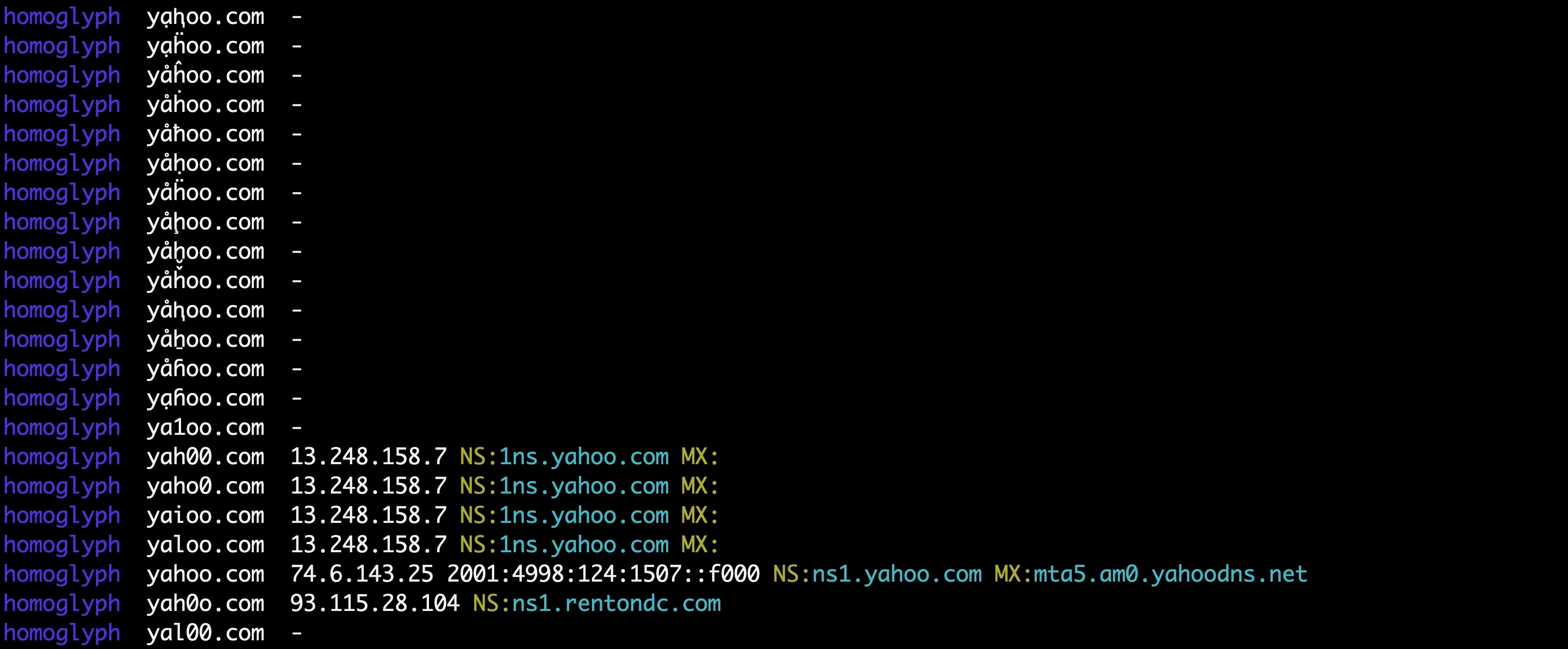
Original Domain : yahoo.com
Homoglyph Domain : yahöö.com
TLD squatting -
Squatter gets a hold of a domain with a different TLD to deceive the target end users. Easiest way to do this is to purchase a country specific domain to a website.
Example :
Original : coderevere.com
TLD squat domains : coderevere.in, coderevere.ae
Combination Squatting OR Combo Squatting -
This is a technique that involves purchasing a domain name which has a combination of the actual domain name and additional characters/word/words. Perpetrators purchase carefully crafted combination domain names to target unsuspecting victims. The primary objective is to make the victims believe the domain they are visiting is legitimate.
Example :
Origin : amazon.com
Combination domains : amazon-shop.com , amazon-us.com
Are there laws that protect us from cybersquatting ?
The ACPA law passed in US(1999) established a cause of action for registering, trafficking in, or using a domain name confusingly similar to, or dilutive of, a trademark or personal name. Read more about it here - https://repository.law.uic.edu/cgi/viewcontent.cgi?article=1120&context=jitpl
So it really depends on the law of the land. US has strict laws against cybersquatting.
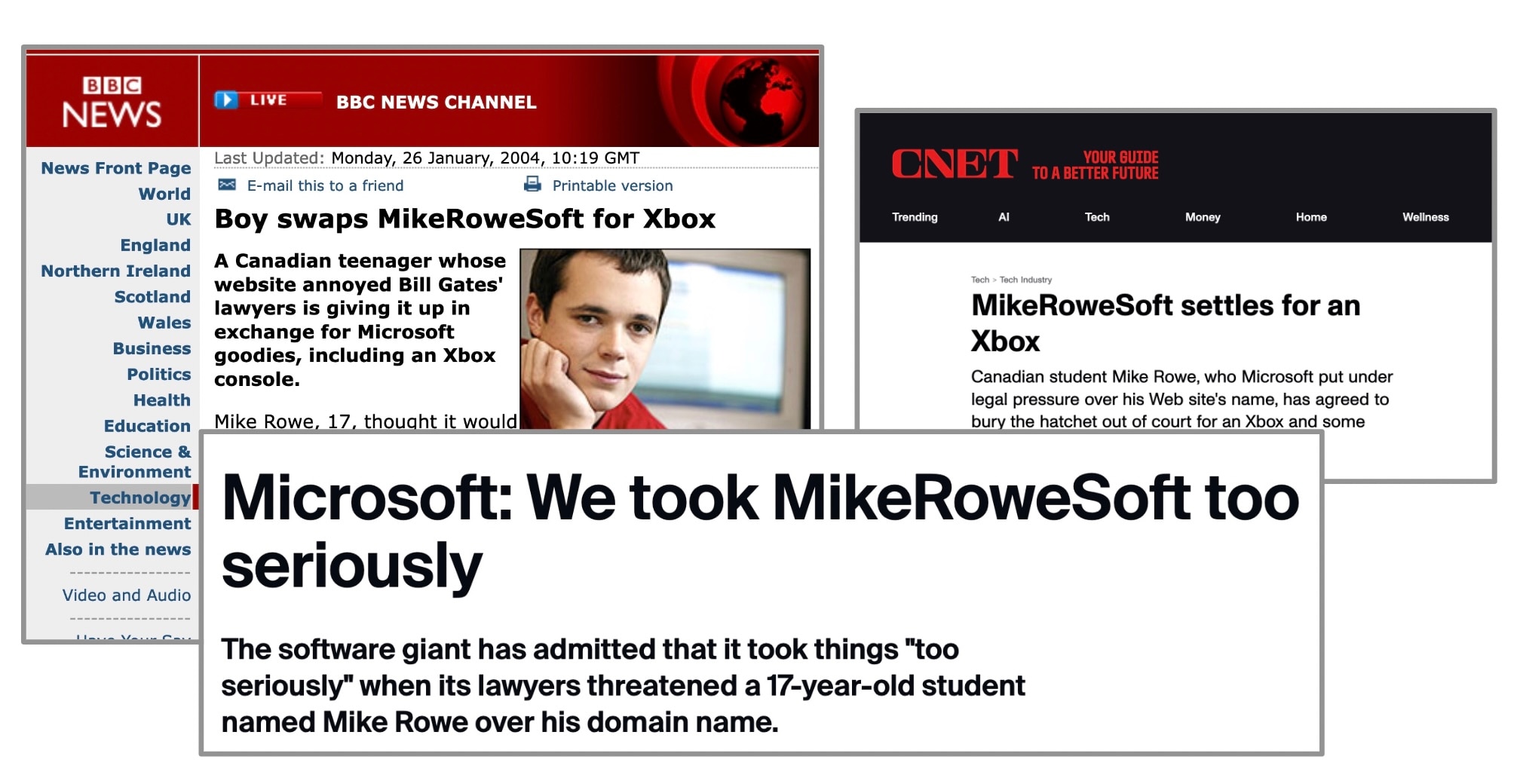
An interesting case that comes to mind is Microsoft vs MikeRoweSoft. Microsoft's canadian lawyers discovered the mikerowesoft.com domain and found it similar to microsoft.com phonetically, served the canadian student Mike with legal documents, asked him to give up this domain for 10 USD who then decided to go to media and asked for 10K USD, he got a lot of support from the online community, got some donations and free lawyer advice as well, almost a textbook underdog story. This was a PR mess for Microsoft, led to an out of court settlement with Mike Rowe who agreed to give up the domain for an Xbox and some additional compensation.
India does not have a dedicated law against cybersquatting(at the time of writing this blog), however there are many incidents in the past where the plaintiffs were able to lean on the general law against trademark infringement(Trademarks Act 1999) etc. and the courts would then proceed to shut down such cybersquatting services/domains.
A couple famous cases where the plaintiff was successful against cybersquatting in India are listed below -
Manish Vij And Ors. vs Indra Chugh And Ors. on 29 January, 2002
https://indiankanoon.org/doc/492412/
Yahoo!, Inc. vs Akash Arora & Anr. on 19 February, 1999
This is the famous Yahoo.com vs Yahooindia.com case, the court restrained the defendants from using this domain.
https://indiankanoon.org/doc/1741869/
Jing Ren is a chinese citizen from Wuhan who has been reported multiple times for cybersquatting, has repeatedly purchased domains such as android.co.in, tiktok.in, amozon.in etc. from the indian registrar, NIXI. Infact he tried selling the android.co.in domain at a premium, the asking price was as high as 20K USD. Google pursued a legal case against him in India as the domain was registered here, Google won this case and took control over this domain.
Another famous incident that comes to mind is google losing control of its TLD, briefly, before regaining control. Sanmay, an ex google employee purchased the google.com domain, had ownership over it for a minute or so. Sanmay noticed google.com was expiring so went ahead with a purchase for this domain, eventually the registrar(also google in this case) cancelled the order and took back control.
Any tools out there that can help ?
Plenty.
Many vendors offer comprehensive brand impersonation protection solutions, check out their offerings.
There are also certain free tools out there that can help you on this path. I recommend the dnstwist tool, you can follow their github link for installation instructions and for a quick start guide - https://github.com/elceef/dnstwist
dnstwist can detect typosquatters, phishing attacks, fraud, and brand impersonation. Useful as an additional source of targeted threat intelligence. This tool generates a comprehensive list of permutations based on a provided domain name, and subsequently verifies whether any of these permutations are in use. Additionally, it can generate fuzzy hashes of web pages to detect ongoing phishing attacks or brand impersonation, and much more!
Please find below a couple dnstwist snapshots that contain a partial list of yahoo.com homoglyphs.
dnstwist --fuzzers "homoglyph" yahoo.com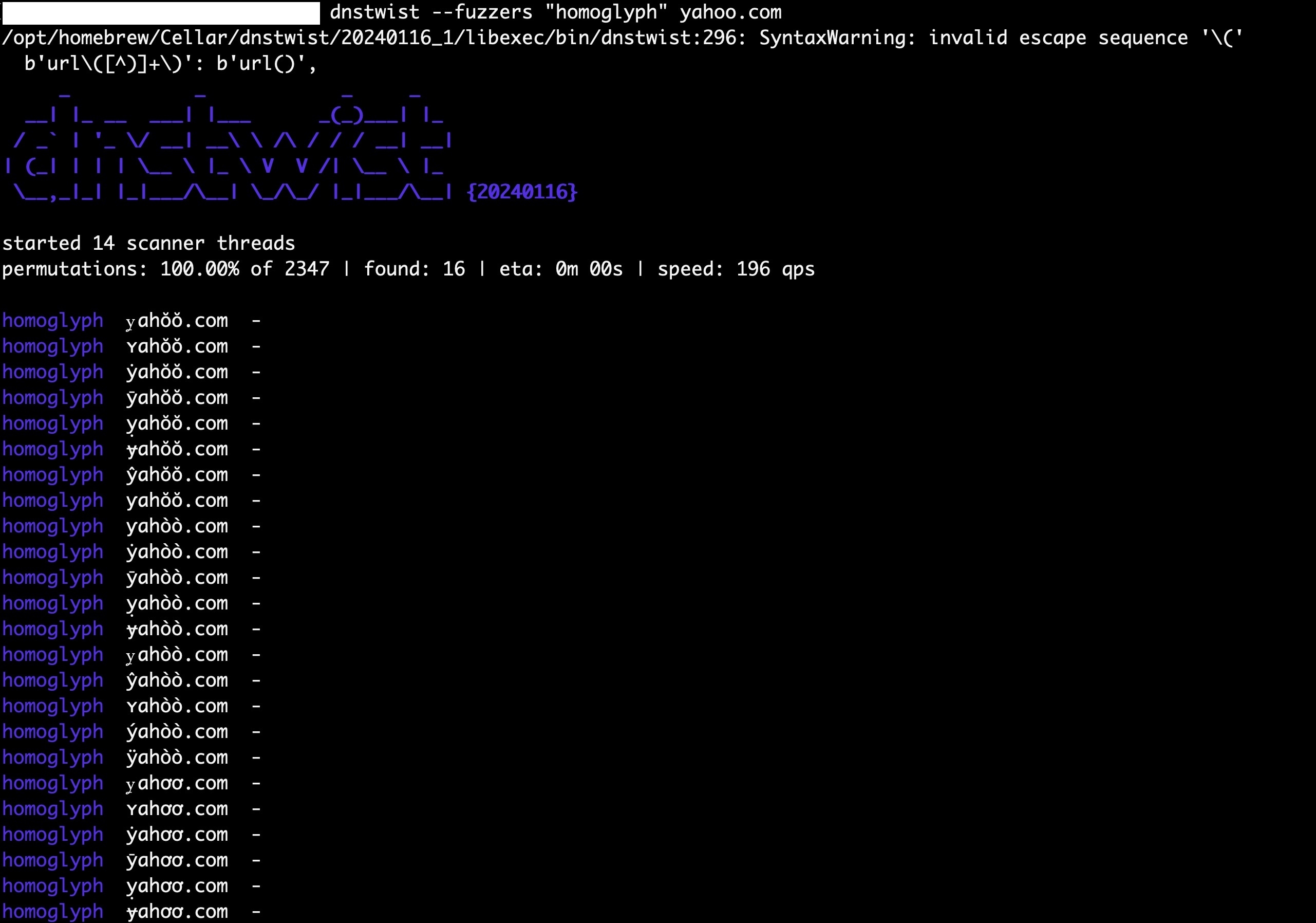


0 Comments